DevSecOps: The rise of a security-first approach to software development

Software development is a complex discipline where security must be treated as equally critical as speed and functionality. As cyber threats become more frequent and sophisticated, traditional approaches that treat security as an afterthought are proving to be inadequate.
Enter DevSecOps, a change that integrates security into every stage of the development lifecycle. By embedding security practices alongside development and operations, organisations can proactively identify vulnerabilities, reduce risk, and deliver robust applications more quickly. This security-first approach is establishing itself as a critical standard for modern software development, ensuring that agility and protection go hand in hand.
What is DevSecOps, and why does it matter?
For years, security was often treated as a final checkpoint, a review performed just before release. This approach slowed down development, created bottlenecks and often allowed vulnerabilities to slip into production, making it costly and disruptive to fix them later on. Today’s applications are more complex than ever; they are cloud-native, distributed and dependent on numerous third-party libraries and services. Supply chain vulnerabilities, misconfigurations and evolving cyber threats mean that late-stage security checks are inadequate.
DevSecOps flips this traditional model – by embedding security in the earliest stages of planning, coding, testing and deployment, organisations can detect issues earlier, reduce costs and maintain rapid delivery. More importantly, it fosters a culture in which everyone takes responsibility for security, rather than leaving it to a specialised team at the eleventh hour.
For years, security was often treated as a final checkpoint, a review performed just before release. This approach slowed down development, created bottlenecks, and allowed vulnerabilities to slip into production, resulting in costly and disruptive fixes later on.
Today, however, the stakes are higher than ever, due to increasingly sophisticated cyber threats, and growing regulatory pressure. Frameworks such as the Cyber Resilience Act are changing how software is developed, particularly for products containing digital elements that are entering the EU market. Compliance requires organisations to embed security throughout the entire software lifecycle rather than just validating it at the end.
See our cybersecurity services and make your business resilient!
Find out moreAt the same time, modern applications are more comple, being cloud-native, distributed, and reliant on numerous third-party libraries and services. Supply chain vulnerabilities, misconfigurations and evolving threats, combined with strict compliance requirements, mean that late-stage security checks are no longer sufficient.
DevSecOps flips this traditional model by embedding security into the earliest stages of planning, coding, testing and deployment. This approach enables organisations to detect issues earlier, reduce costs, maintain rapid delivery and ensure ongoing compliance with emerging regulations. Furthermore, it fosters a culture in which everyone takes responsibility for security, rather than leaving it to a specialised team at the last minute.
From DevOps to DevSecOps – adding security to the development pipeline
DevOps transformed software development by breaking down the traditional barriers between development and operations teams, enabling faster release cycles through practices such as continuous integration and continuous delivery, infrastructure automation and close cross-team collaboration. The main goal of DevOps is to speed up software delivery while ensuring system reliability and operational stability.
While DevOps emphasises speed, automation and continuous deployment, DevSecOps ensures that security controls are systematically integrated into every phase of the pipeline, from planning and coding to testing, deployment and monitoring. Rather than treating security as a separate review phase carried out late in the development cycle, DevSecOps incorporates continuous security validation into the development workflow.
There are several characteristics that distinguish DevSecOps from traditional DevOps implementations.
- Shared responsibility
In conventional DevOps environments, security responsibilities are often primarily assigned to specialised security teams. DevSecOps, however, promotes a shared responsibility model in which developers, operations engineers, and security specialists collaborate to identify and mitigate risks throughout the lifecycle. - Integrated security controls
DevSecOps incorporates automated security mechanisms directly into CI/CD pipelines. These include practices such as Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), Software Composition Analysis (SCA), container image scanning and infrastructure-as-code (IaC) security validation. - Continuous risk management
Rather than relying on periodic audits or post-development security testing, DevSecOps enables the continuous assessment of vulnerabilities, misconfigurations and dependency risks. Automated feedback loops allow issues to be identified and resolved earlier in the development process.
Key differences: DevOps vs. DevSecOps
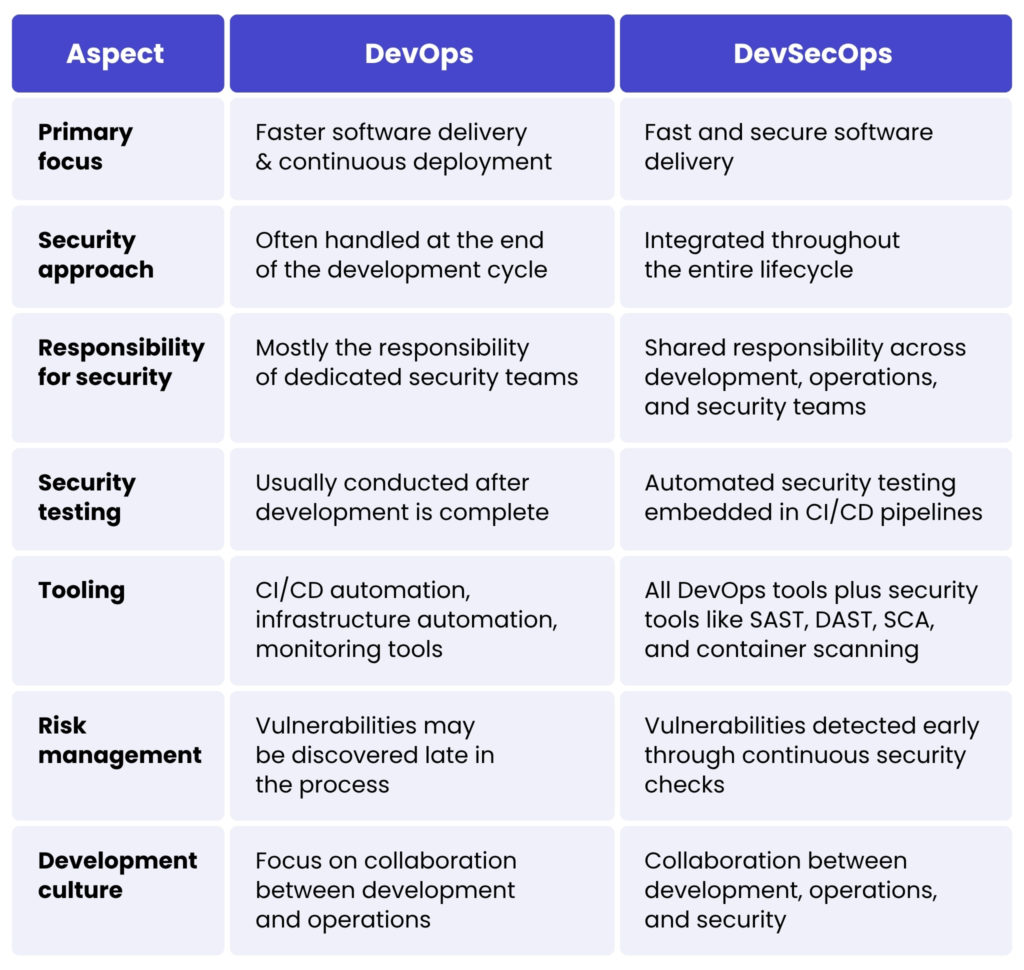
Ultimately, DevSecOps does not replace DevOps, but extends its principles to address the growing importance of security in complex, cloud-native environments. By integrating security controls into automated delivery pipelines and fostering collaboration between development, operations and security teams, organisations can maintain the speed and agility of DevOps while ensuring software is delivered securely and resiliently.
The shift-left approach in DevSecOps
One of the most fundamental principles of DevSecOps is the concept of ‘shifting left’. In the context of the software development lifecycle, ‘left’ refers to the initial stages of the process, such as planning, design and coding, when decisions regarding architecture, dependencies and implementation are initially made. Traditionally, security validation occurred near the end of the development cycle, typically during dedicated testing phases or pre-release audits. The shift-left approach redefines this model by introducing security considerations at the earliest possible stage of development.
In practical terms, shifting security left involves embedding security practices directly into design reviews, development workflows and developer toolchains. Security requirements are defined during the planning phase, threat modelling becomes part of the system design process and developers use integrated tools that automatically analyse code for vulnerabilities as it is written. Automated checks such as static code analysis, dependency vulnerability scanning, and policy validation are increasingly included in modern development environments, allowing potential risks to be identified long before the software reaches production.
This early integration of security significantly improves the efficiency of vulnerability management. Issues detected during the design or development stages can usually be resolved swiftly with minimal disruption, often requiring only minor adjustments to the code or configuration. By contrast, vulnerabilities discovered late in the release cycle, or after deployment, can require extensive rework, emergency patches, or even architectural changes. Consequently, organisations that adopt shift-left practices often experience a substantial reduction in remediation costs and operational risk.
Another important outcome of this approach is that it empowers developers. Rather than relying solely on downstream security teams to identify and resolve issues, developers can now gain direct visibility into potential vulnerabilities within their own code. Integrated feedback mechanisms, such as automated alerts within IDEs or CI pipelines, enable engineers to address security concerns in real time as they develop features. This accelerates remediation and fosters greater awareness of secure coding practices.
Integrating security across the delivery pipeline
In order to successfully implement DevSecOps, security must be embedded throughout the entire software delivery lifecycle, rather than being introduced as a separate, final step. The DevSecOps lifecycle incorporates automated security controls, testing procedures and monitoring capabilities into every stage of the DevOps pipeline. This ensures that potential vulnerabilities, misconfigurations and compliance issues are continuously identified and addressed.
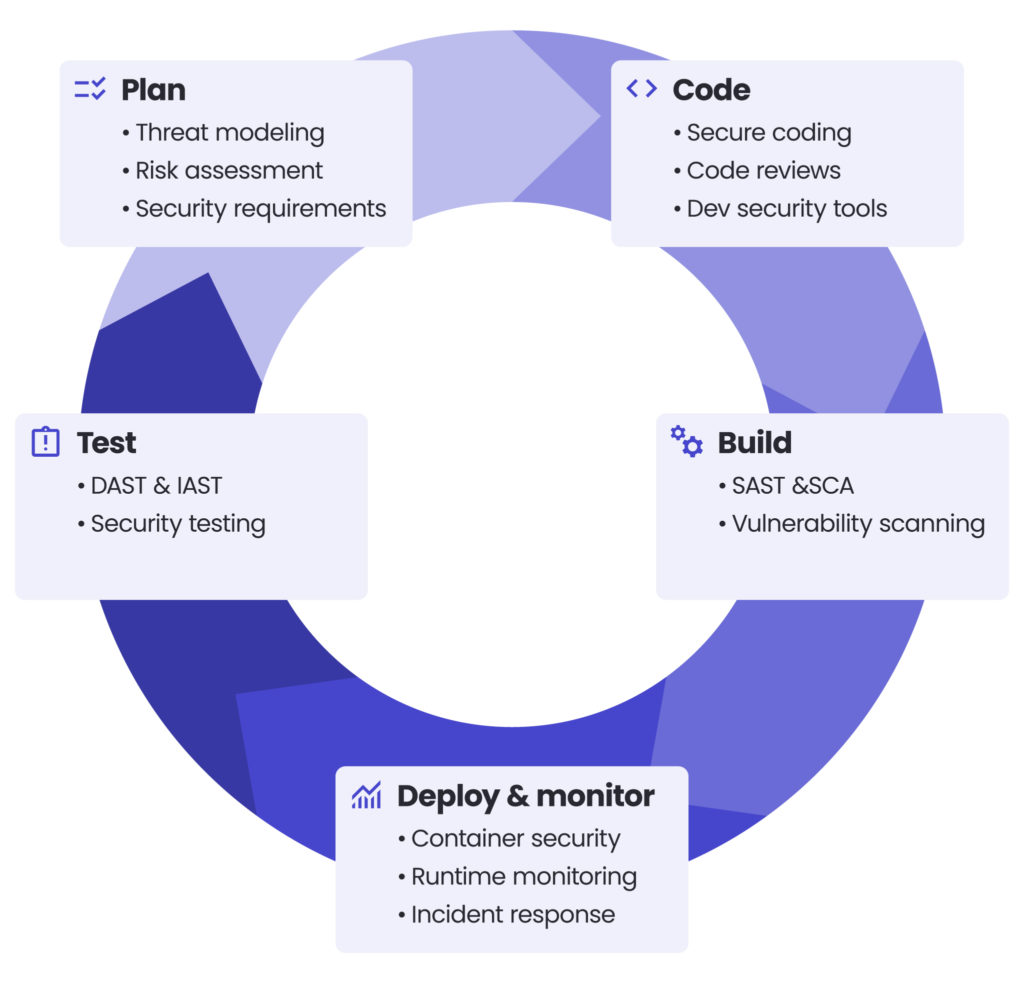
1. Plan
The lifecycle begins with security-aware planning, during which potential risks are evaluated prior to the start of development. At this stage, teams carry out threat modelling to identify potential attack vectors and security vulnerabilities in the proposed architecture. This process enables developers and security specialists to anticipate risks relating to data flows, authentication mechanisms, external integrations and infrastructure components.
Alongside threat modelling, organisations carry out risk assessments to prioritise potential vulnerabilities based on their likelihood and impact. Security requirements, such as encryption standards, authentication protocols or regulatory compliance obligations, are then formally defined and incorporated into the system design and development roadmap. Defining these requirements early on ensures that security is considered a fundamental design principle rather than an afterthought.
2. Code
During the development phase, security practices are integrated directly into the coding workflow. Teams adopt secure coding standards to guide developers in avoiding common vulnerabilities, such as injection flaws, insecure authentication or improper error handling.
Code quality and security are reinforced further through peer code reviews, in which developers evaluate each other’s work for both functionality and adherence to security best practices. Additionally, automated linting tools and developer security plugins integrated into IDEs can identify potential issues, such as unsafe functions, exposed credentials or insecure dependencies, as code is written. These automated checks enable developers to identify and resolve security issues at an early stage in the development process.
3. Build
The build stage incorporates automated security analysis into the continuous integration pipeline. One of the primary techniques used here is static application security testing (SAST), which analyses source code, bytecode or compiled binaries to identify potential vulnerabilities without executing the application.
Another critical practice is software composition analysis (SCA). Modern applications often rely heavily on open-source libraries and third-party dependencies, which may contain known vulnerabilities. SCA tools automatically scan project dependencies against vulnerability databases to identify outdated or insecure components.
Furthermore, dependency vulnerability scanning ensures that any external packages integrated into the build process are continuously evaluated for any newly discovered security issues.
4. Testing
During the testing phase, security validation moves beyond static analysis to evaluate the behaviour of the application during execution. Dynamic Application Security Testing (DAST) involves simulating external attacks on running applications to identify vulnerabilities such as authentication weaknesses, configuration issues or input validation flaws.
Some organisations also use Interactive application security testing (IAST), which combines static and dynamic testing elements by monitoring application behaviour during functional testing. This approach provides deeper insight into how vulnerabilities manifest in real runtime conditions.
Alongside automated scanning, teams often carry out security-focused integration tests to verify that authentication mechanisms, access controls and data protection measures operate correctly across system components.
5. Deploy & monitor
Responsibilities for security do not end once the application has been deployed. In the DevSecOps model, runtime security monitoring plays a critical role in identifying emerging threats and operational vulnerabilities.
Prior to deployment, teams conduct container security checks and configuration scanning to prevent misconfigurations or exposed services from being introduced by container images, infrastructure configurations, and orchestration settings. Once the application is running, continuous monitoring systems analyse logs, system metrics and network activity to detect anomalous behaviour that may indicate a security incident.
Effective DevSecOps implementations also include incident detection and response mechanisms, enabling teams to swiftly investigate and mitigate potential breaches. Importantly, insights gathered from runtime monitoring are fed back into the development pipeline through continuous feedback loops. This enables teams to improve security controls, update configurations and refine development practices over time.
Essential tools and automation in DevSecOps
Although DevSecOps is frequently regarded as a cultural and procedural change, its practical implementation depends heavily on automation and specialised security tools. In modern software development environments characterised by rapid release cycles, distributed architectures and complex dependency chains, manual security checks are insufficient. DevSecOps addresses this challenge by integrating automated security controls directly into CI/CD pipelines, enabling continuous and scalable vulnerability detection throughout the development lifecycle.
Automation plays a central role in ensuring consistent security validation without slowing down delivery. Security tools are embedded within development workflows so that code, configurations, and dependencies are automatically analysed whenever changes are introduced. This approach enables development teams to identify potential vulnerabilities early on, receive immediate feedback and resolve issues before they propagate further into the pipeline.
A typical DevSecOps toolchain incorporates various categories of security technology, each of which addresses different layers of the application stack.
Static application security testing (SAST)
SAST tools analyse source code, bytecode or compiled binaries without executing the application. They scan codebases for patterns associated with common vulnerabilities, such as injection flaws, insecure authentication mechanisms or improper error handling. As SAST operates during the development and build phases, it allows developers to identify security issues before the application is deployed.
Dynamic application security testing (DAST)
Unlike static analysis, DAST evaluates applications while they are running. By simulating external attacks against deployed applications, DAST tools can identify vulnerabilities, such as misconfigurations, authentication weaknesses and input validation issues, that may not be apparent through static code inspection alone.
Software composition analysis (SCA)
Modern applications often depend on a large number of open-source libraries and third-party dependencies. While these components can accelerate development, they can also introduce security risks if vulnerabilities exist within the external code. SCA tools continuously scan project dependencies against vulnerability databases and alert teams when outdated or insecure components are detected. This capability is particularly important for managing risks in the software supply chain.
Security for containers and Kubernetes
As organisations increasingly adopt containerised and cloud-native architectures, security measures must be extended to encompass runtime environments as well as application code. Container security tools scan container images for vulnerabilities, misconfigurations and outdated packages prior to deployment. Orchestration platforms such as Kubernetes offer additional security controls to help enforce policies related to network segmentation, access permissions, and workload isolation.
Infrastructure-as-Code (IaC) security scanning
The provisioning of infrastructure is becoming increasingly automated through the use of IaC technologies, such as Terraform, CloudFormation and ARM templates. While this approach improves scalability and consistency, misconfigurations within infrastructure definitions can expose systems to significant risk. Security scanning tools analyse infrastructure templates to detect insecure configurations, such as publicly exposed storage, overly permissive access controls or unencrypted data resources, before infrastructure is deployed.
Integrating security feedback into developer workflows
For security tools to be effective, they must integrate seamlessly into the environments in which developers work. These environments include integrated development environments (IDEs), version control systems, and CI/CD platforms. Automated alerts, pull request checks and pipeline feedback give developers immediate insight into potential security issues.
Importantly, DevSecOps tooling is designed to act as guidance for developers rather than as obstacles. Rather than hindering development progress with manual security reviews, automated tools offer continuous guidance to help developers adhere to secure coding practices while maintaining high delivery velocity.
Wrapping up
As software systems become increasingly complex and interconnected, it is no longer sufficient to treat security as a final checkpoint. DevSecOps addresses this challenge by integrating security practices into every stage of the development lifecycle, from planning and coding to testing and deployment. Automation, continuous testing, and integrated security tools enable teams to detect vulnerabilities earlier and resolve them more efficiently.
By combining the speed of DevOps with a proactive security approach, DevSecOps enables organisations to deliver software that is faster, more resilient, and secure.
Adopting DevSecOps requires a change in the way that teams approach software development. This involves integrating security into CI/CD pipelines, providing developers with automated security checks and encouraging collaboration between development, operations and security teams. Organisations can then significantly strengthen their security posture while maintaining rapid delivery.
Contact our experts and begin by identifying opportunities to introduce security earlier in your development process, then build a pipeline that prioritises secure software delivery.
DevSecOps is an approach that integrates security into every phase of software development, rather than treating it as a final step. It ensures that applications are built, tested and deployed with security in mind from the very beginning.
While DevOps focuses on speed and efficiency, DevSecOps adds a strong security layer across the entire pipeline. Security becomes a shared responsibility and is continuously validated through automated tools and processes.
Modern applications are complex, cloud-based and highly dependent on third-party components, which increases security risks. DevSecOps helps organisations proactively identify vulnerabilities and stay compliant with evolving regulations.
Shift-left means introducing security practices early in the development lifecycle, such as during planning and coding. This allows teams to detect and fix vulnerabilities sooner, reducing costs and delays.
DevSecOps improves security, reduces remediation costs and accelerates delivery by catching issues early. It also fosters a culture where development, operations and security teams collaborate more effectively.
arrow_circle_rightcontact us
Focus on your core business, while we manage your IT infrastructure maintenance
arrow_circle_right our blog









